Tutorial Setting Up a VPN for Secure Internet Browsing
How to Set Up a VPN
Why does your business need a VPN?
At their most basic, VPNs protect businesses and users and their confidential data. Here are other reasons why your business could benefit from a VPN:
Convenience
VPNs are a convenient way to give employees, including remote workers, easy access to your business network without having to be physically presentwhile maintaining the security of private networks and business resources.
Better security
Communication with a VPN connection provides a higher level of security compared to other methods of remote communication, keeping private networks closed to people who dont have authorized access. The actual geographic locations of users are protected and not exposed to public or shared networks like the Internet.
Easier administration
Its easy to add new users or groups of users to networks using flexible VPN software tools. That's good for businesses that are growing faster than their budgets since it means you can often expand network footprints without adding new components or building complicated network configurations.
Are there downsides to using VPNs?
A VPN's success depends on other parts of your network infrastructure. Here are factors that could cause performance issues for your VPN:
Configuration security risks
Design and implementation of a VPN can be complicated. If youre not sure how to keep it up and running safely, consider bringing in an experienced network security professional to make sure VPN security hasnt been compromised.
Reliability
Since VPN connections run off the Internet, you need to choose an Internet service provider (ISP) that consistently delivers excellent service with minimal to no downtime.
Scalability
If you need to add new infrastructure or create new configurations, you may run into technical problems due to incompatibilityespecially if you're adding new products from different vendors.
Slow connection speeds
If you're using a VPN client that provides free VPN service, your connection speed may be slow, as these providers do not usually offer high-speed connections. Consider whether the speed is sufficient for business needs.
Should you create your own VPN, or buy one?
Instead of trying to build one yourself, you can buy a prebuilt VPN solution. If you're shopping for VPN solutions, ask questions about the ease of configuration.
Steps for setting up a VPN
6 steps to set up a VPN
Step 1: Line up key VPN components
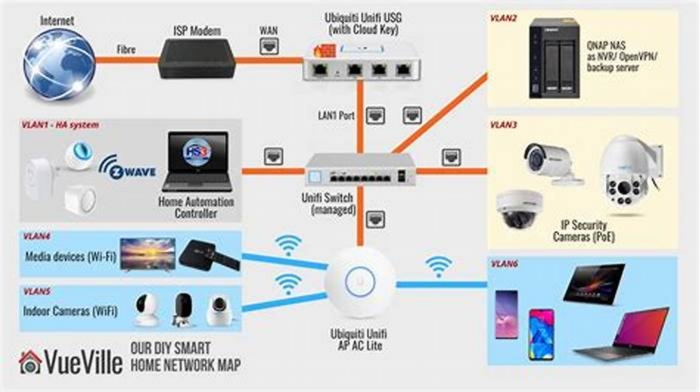
To get started, you'll need a VPN client, a VPN server, and a VPN router. The downloadable client connects you to servers around the world, so employees everywhere can access your small business network. The client can be used on devices like smartphones and laptops, even if workers are using public Wi-Fi networks.
To secure and encrypt all network traffic, you'll also need a VPN router. Many routers come with VPN clients built-in.
Step 2: Prep devices
On occasion, VPN clients can conflict with other clients, or fail to work properly. It's a good idea to prepare your network system before you set up a VPN so that you can avoid problems down the road.
As a first step, uninstall any existing VPN client software that you dont need. In theory, the VPN clients should be able to work well together, but competing clients can also be a source of problems, so its best to remove them.
This is also a good time to consider network configuration. If you plan to install a VPN for workers who'll access online resources in several wayssuch as Wi-Fi, 4G modems, and wired connectionsyou may need to spend more time configuring the VPN client. Simplifying networks by unplugging unused devices can help.
Step 3: Download and install VPN clients
The simplest way to get your VPN up and running is to install clients from your VPN provider. However, they may not offer software for every platform you need, such as Windows, iOS, and Android. Even if they don't, it's better to install what they offer first and then confirm that your VPN account is operating correctly.
Look for the "downloads" page on your VPN provider's website. You should also download apps for the mobile devices that your workers use since youll want to protect connections from as many devices as possible.
If the initial client you install works right off the bat, then you can contact the VPN provider about clients for other platforms. And if you cant log in at all, then you can pass along that information to the VPN provider's support team.
Step 4: Find a setup tutorial
If, for some reason, your VPN provider doesn't offer software for the devices your business uses, check the provider's website for guides on manual setup. Hopefully, you'll find the documentation you need. If you don't, search for other providers' setup guides that use the same devices.
For example, if your business uses Chromebooks, you can search for tutorials specifically for these devices.
Step 5: Log in to the VPN
After you install the VPN client apps, it's time to enter login information. In general, the username and password will be the ones you used when you signed up with the VPN provider, although some companies ask you to create a separate login for the VPN client itself.
Once you're logged in, the VPN app usually connects to the server nearest to your current location.
Step 6: Choose VPN protocols
VPN protocols decide how data is routed between your computer and the VPN server. Some protocols help improve speed, while others help improve data privacy and security.
OpenVPN
This is an open-source protocol, which means you can view its code. OpenVPN is also rapidly becoming an industry standard.
L2TP/IPSec
The Layer 2 Tunnel Protocol is another popular protocol. It has strong security protections and is often bundled with the IPSec protocol, which authenticates and encrypts packets of data sent over the VPN.
SSTP
The Secure Socket Tunneling Protocol is fully integrated with the Microsoft operating system.
PPTP
Point-to-Point Tunneling Protocol is one of the oldest VPN protocols. But it is becoming less widely used since there are faster and more secure protocols available.
Step 7: Troubleshoot
Usually, your VPN provider's client will start working right away. But if that's not the case, try these steps:
- Shut down and reopen the client and try rebooting your device.
- If you have any other VPN software running, make sure you're disconnected, then close it down.
VPN clients need appropriate software drivers to work correctly. In some cases, you can click on the "repair" setting to reload drivers. Check the settings page to see if this feature is available.
If you're having trouble logging in, double-check your login credentials. Some VPN clients generate their own logins, and some let you choose your own.
Be sure you're using the correct login, and if necessary, read any welcome emails or quick-start guides you may have received from the provider.
You can also try switching servers. Choose to connect to a different server that's close to your physical location.
Another option: Try connecting with different protocols, assuming the VPN client allows you to change them. For example, you can use OpenVPN using TCP, then switch to L2TP and PPTP.
If you're still running into problems, other software programs may be the culprit. Sometimes, firewalls or security software can disrupt VPN connections. You can temporarily disable software that might be causing the problemjust make sure to turn it back on once you connect so you dont leave critical business systems vulnerable to attack.
Step 8: Fine-tune the connection
Once you have the basics out of the way, it's time for improvements. Make sure the settings you've applied to the VPN suit your business's needs.
For example, decide whether you'd like the VPN to run as soon as people start their devices. This may be a good idea if you need the protection of a VPN all the timefor example, if most people work outside the office. But if you think that you'll only need to use the VPN occasionally, you can set it to launch only when required, freeing up network resources for other uses.
Another fine-tuning option is to choose commonly used servers as your defaults or "favorites." This can save you a bit of time since you and other employees won't have to search for preferred servers every time you connect.
You may also want to turn on the "kill-switch" if your VPN provider offers it. The kill-switch is designed to prevent a device from sending or receiving data if the VPN becomes disconnected.
How to Access the Dark Web Safely Step-by-Step
On the internet, Googles reach barely scratches the surface. So, if you want to know how to access the dark web safely, you need to understand that the vast majority of the dark web, or dark net, is only accessible through the Tor browser. Google uncovers less than 0.2% of the entire web. Its like an iceberg The visible tip above water, known as the surface web represents the familiar, searchable content. But lurking beneath lies the expansive, mysterious deep web ordark net the gigantic submerged part that remains invisible to standard searches.
The dark web, an even more puzzling sublayer, exists within this hidden world. Here, stealth and secrecy rule. Its designed as an environment to elude detection, where site owners and visitors hide their identities. And while the dark web isnt synonymous with illicit activities, its undeniably the breeding ground for the internets black markets, hacker forums, malware vendors, and other illegal activity.
Our rigorous research and testing have revealed revealing truths and busted myths.Well navigate this intricate maze with you, uncovering its secrets while ensuring your online safety.
What is the dark web?
The dark web, or dark net, is a small part of the deep web that is kept hidden on purpose. Websites and data on the dark web do typically require a special tool to access.
The type of sites most commonly associated with the dark web are marketplaces where illicit goods such as narcotics, firearms, and stolen credit card numbers are bought and sold. The darkest corners are used to hire hitmen, engage in human trafficking, and exchange child pornography.
More than that, though, the dark web contains content and data that can be accessed anonymously. It could be a blog, forum, chat room, or private gaming server.
The beauty of the dark net is anonymity. No one knows who anyone else is in the real world, so long as they take the necessary precautions. Users identities are safe from the prying eyes of governments and corporations.
Journalists and whistleblowers, including Edward Snowden himself, often use the dark web and Tor to exchange sensitive information. For instance, the Ashley Madison data dump was posted to a site only accessible to Tor users.
How to access the Dark Web safely
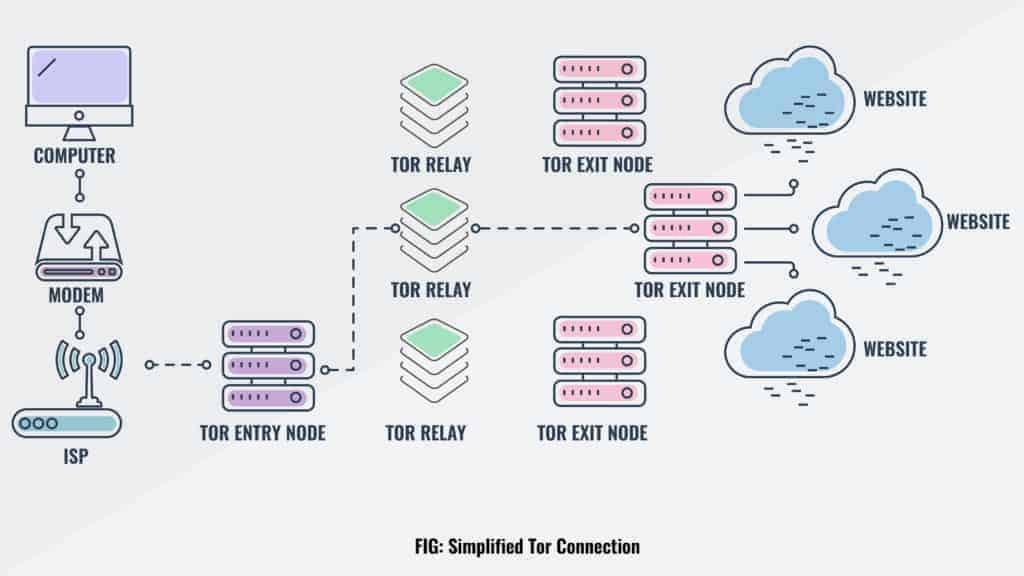
Using Tor is a must. Tor is a network of volunteer relays through which the users internet connection is routed. The connection is encrypted, and all the traffic bounces between relays located around the world, making the user anonymous.
Related post: Dark Web Monitoring Tools
How to get the Tor Browser
The easiest way to access Tor is through a special browser, known as the Tor Browser. You can download and install it for free. You might want to hide your Tor Browser download using a VPN and your existing browsers private/incognito mode.
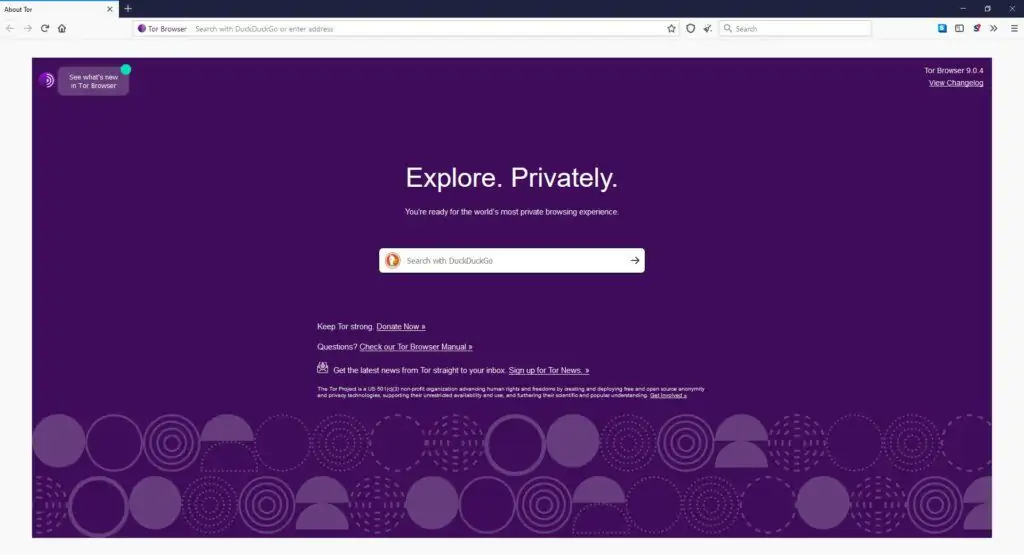
Based on Firefox, the Tor Browser lets you surf both the clear web and the dark web. All your traffic is automatically routed through the Tor Network. Make sure to download the Tor Browser only from the official website to avoid downloading malware, spyware, or some other virus to your device.
Officially, the Tor Browser is only available on Windows, Mac, Android, and Linux. Many experts advise against using third-party mobile browsers that utilize the Tor Network. Sorry, iOS users. There are no standard web browsers that can be used to access dark web content.
Added security: Use a VPN
Internet providers and websites can detect when Tor is being used because Tor node IPs are public. Although websites cant identify you and ISPs cant decrypt your internet traffic, they can see that Tor is being used. This can raise suspicions and draw unwanted attention.
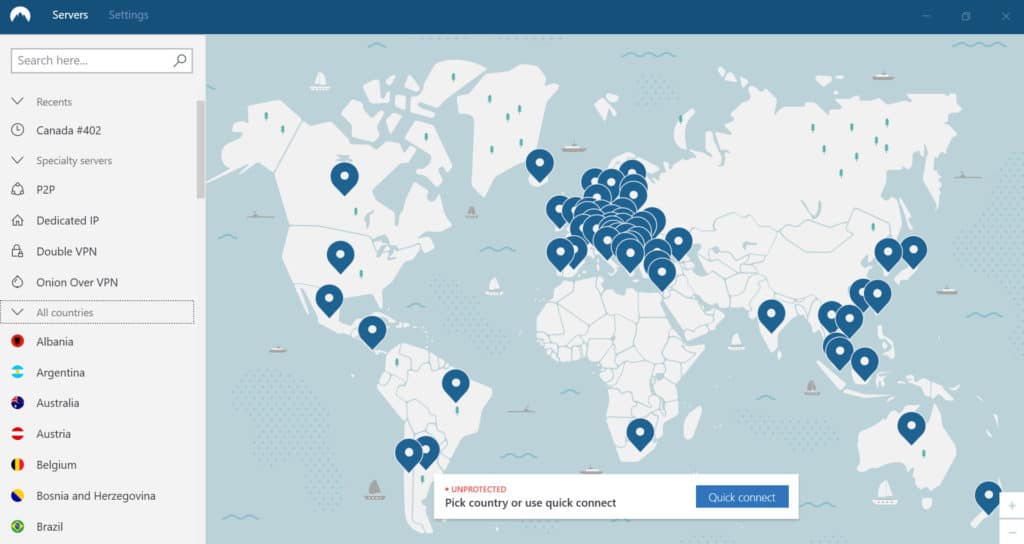
If you want to use Tor privately, you can use either a VPN or Tor Bridges (Tor nodes that are not publicly indexed). Tor users in the USA, in particular, may want to use a VPN, which will be faster and more reliable.
When using a VPN for the dark web, your ISP will not be able to see that you are connected to a Tor node, only an encrypted tunnel to a VPN server.
WANT TO TRY THE TOP VPN RISK FREE?
NordVPN is offering a fully-featured risk-free 30-day trial if you sign up at this page. You can use the VPN rated #1 for the dark web with no restrictions for a monthgreat if you want to try this no-log provider's Onion over VPN servers for yourself.
There are no hidden terms or conditionsjust contact support within 30 days if you decide NordVPN isn't right for you and you'll get a full refund. Start your NordVPN trial here.
It would also be smart to install antivirus software. Even when using security measures and your own common sense, accessing deep web content still poses a risk. Antivirus will ensure that any viruses or malware downloaded from the dark web are removed.
Navigating the dark net
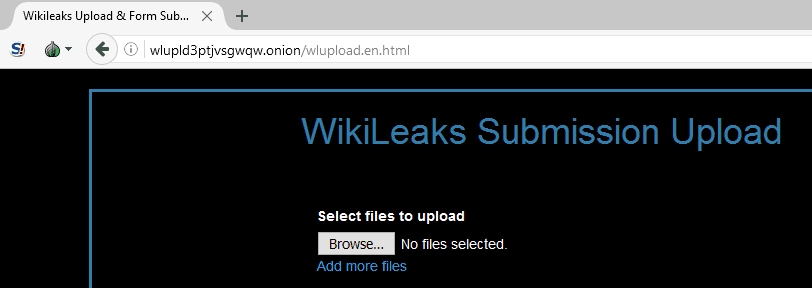
Now that you have Tor, you can access the dark web. Dark net websites are called Tor hidden services, and they can be distinguished from normal websites by their URLs.
Instead of .com or .org, dark web addresses can be distinguished by the top-level domain, .onion.
Obviously, finding these .onion websites is the first challenge, as they wont show up in Google search results. You cant just Google Silk Road and hope to land on the dark website.
A handful of dark web search engines that do index .onion sites include NotEvil, Ahmia, Candle, and Torch. There are also directories like dark.fail.
BUT DONT TAKE MY WORD FOR IT
Always exercise extreme caution when using publicly posted onion URLs. If you cant get a personal recommendation from someone you trust, verify the URL from multiple different sources.
The dark web has no shortage of criminal activity, scams, phishing sites, suspicious links, and malware designed to trick newbies. Links posted to the clear web, in particular, are often malicious. And because theres very little use of HTTPS on the dark net, verifying whether or not a website is genuine using an SSL certificate is not feasible.
Reddit is also a valuable resource for finding the dark net or deep website youre looking for. Try the /r/deepweb, /r/onions, and /r/Tor subreddits.
Anonymity is in your hands
You can now safely browse dark web websites and hidden wikis, but if you plan to do anything more than that, youll need to take several precautions. If you plan to make a purchase on a dark net marketplace or dark web commerce sites, youll need to create a fake identity. That means setting up encrypted email with a new email address, encrypting messages with PGP, using a pseudonym, setting up an anonymous Bitcoin wallet, disabling Javascript in Tor Browser, researching vendors, and more. Remember only to make purchases using digital currencies and never provide any online banking login details.
Again, we cant emphasize enough that security and anonymity are paramount to those on dark websites. Your ISP and the government might not be able to view your activity when on the Tor Network, but they do know you are on the Tor Network, and that alone is enough to raise eyebrows. In fact, a recent judgment by the US Supreme Court denoted that simply using Tor was sufficient probable cause for law enforcement to search and seize any computer around the world.
Another vital precaution is to ensure that your .onion URLs are correct. Onion URLs generally contain a string of seemingly random letters and numbers. Once you are certain that you have the correct URL, save it in an encrypted notethe Tor browser will not cache it for later. Otherwise, theres a good chance of falling victim to a phishing scam like this fake Bitcoin mixer.
We highly recommend employing another layer of security via a VPN.
What is the deep web?
The deep web is often confused with the dark net. Put simply, the deep web is all of the information stored online that isnt indexed by search engines. You dont need any special tools or a dark net browser to access most of the deep web; you just need to know where to look. Specialized search engines, directories, and wikis can help users locate the data theyre looking for.
Most of that information is hidden simply because the vast majority of users wont find it relevant. Much of it is tucked away in databases that Google is either not interested in or barred from crawling. A lot of it is old and outdated. The contents of iPhone apps, the files in your Dropbox account, academic journals, court records, and private social media profiles are all examples of data that Google doesnt necessarily index but still exist on the internet.
Many of the best general deep web search engines, like Alltheweb, DeeperWeb, and CompletePlanet, have shut down or been acquired. Only a couple will offer more complete results than Google, Bing, or Yahoo:
- Dogpile A metasearch engine that compiles results from several other search engines, removes duplicates and gives results
- The WWW Virtual Library The original index of the web, but more of a directory than a search engine.
These are okay, but specialized search engines tend to be better than general ones for finding info on the deep web. If youre looking for a court case, for example, use your state or countrys public records search. If you need academic journals, check out our article on using deep web search engines for academic and scholarly research. The more specific you can be, the better, or else youll just end up with the same search results that you would find on Google. If you need a specific file type, like an Excel file or a PDF, learn how to specify searches for that type of file (e.g., type filetype:PDF in your query).
How can I differentiate legitimate services from scams on the dark web?
Here are some tips to help you differentiate between legitimate services and scams on the dark web:
- Research: Before using any service on the dark web, do your research. Look for reviews and feedback from other users to get an idea of the legitimacy of the service. Be wary of services that have no reviews or feedback.
- Payment: Be cautious of services that require payment upfront or ask for payment through untraceable methods such as cryptocurrency. Legitimate services will usually offer secure payment options. Avoid providing credit card details or anything that can personally identify you.
- Too good to be true: Be wary of services that offer unrealistic deals or prices. If it seems too good to be true, it probably is.
- Communication: Legitimate services will usually have a way to contact them for support or questions. If a service has no way to contact them or does not respond to inquiries, it may be a scam.
- Reputation: Check the websites or services reputation on the dark web. If it has a bad reputation or is known for scams, its best to avoid it. Some of these sites include illegal content and have been known to be monitored by law enforcement agencies.
- Personal Information: Be cautious of services that ask for personal information such as your name, address, or social security number. Legitimate services will require only minimal information.
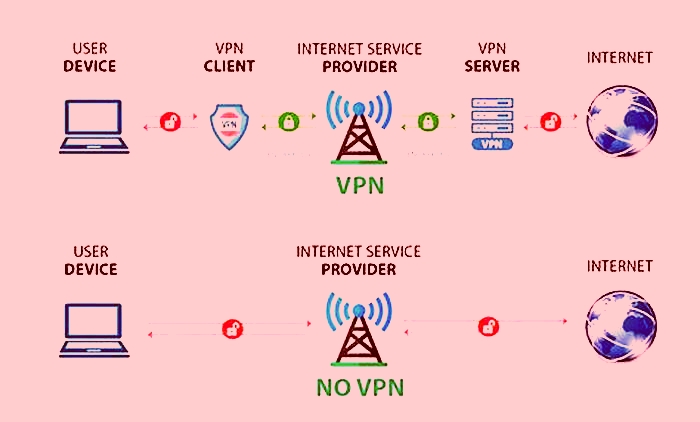
VPN over Tor versus Tor over VPN
A VPN allows a user to encrypt all the internet traffic traveling to and from his or her device and route it through a server in a location of that users choosing. A VPN, in combination with Tor, further adds to the security and anonymity of the user.
While somewhat similar, Tor emphasizes anonymity, and a VPN emphasizes privacy.
Combining them reduces risk, but theres an important distinction in how these two tools interact. Lets first discuss Tor over VPN.
If you connect to your VPN and fire up Tor Browser, youre using Tor over VPN, this is by far the most common method. All your devices internet traffic first goes to the VPN server, then it bounces through the Tor Network before ending up at its final destination. Your ISP only sees the encrypted VPN traffic, and wont know youre on Tor. You can access .onion websites normally.

Tor over VPN requires you to trust your VPN provider, which can see that you are using Tor and keep metadata logs, though it cant actually see the content of your encrypted Tor traffic. A logless VPN, which doesnt store any traffic logs nor session logs is highly preferable. Traffic logs contain the content of your internet traffic, such as search queries and websites you visited, while session logs contain metadata like your IP address when you logged into the VPN, and how much data was transferred. Traffic logs are a bigger concern than session logs, but neither are good.
For built-in Tor over VPN functionality, NordVPN operates specialized servers that automatically route you through the Tor network. You dont even need to use Tor Browser, but keep in mind other browsers can still pass identifying information through the network. Alternatively, theres IPVanish who claim to be the worlds number one VPN for Tor and comes highly recommended, you can save 60% on the annual plan here.
DEAL ALERT: NordVPN is running a 2-year deal with a huge 62% discount here.
Tor over VPN also doesnt protect users from malicious Tor exit nodes. Because Tor nodes are made up of volunteers, not all of them play by the rules. The final relay before your traffic goes to the destination website is known as the exit node. The exit node decrypts your traffic and thus can steal your personal information or inject malicious code. Additionally, Tor exit nodes are often blocked by websites that dont trust them, and Tor over VPN cant do anything about that, either.
Then theres the less popularVPN over Tor,which is advised against by the official Tor Project. Only two VPN providers that we know of, AirVPN and BolehVPN, offer this service, although neither of these score highly for speeds. In this case, the order of the two tools is switched. Internet traffic first passes through the Tor Network, and then through the VPN. This means the VPN provider doesnt see your real IP address and the VPN protects you from those bad exit nodes.
The big downside is that your ISP will know you are using Tor, which is cause for concern in some places and will put many people off using this method. In this instance, too, it is important to use a loglessVPN and pay with Bitcoin if you can to stay anonymous. The VPN over Tor technique is also susceptible to an end-to-end timing attack, though its highly unlikely.
Tor over VPN requires you to place some trust in your VPN provider but not your ISP, and is best if you want to access .onion websites. VPN over Tor requires you to place trust in your ISP but not your VPN and is best if you want to avoid bad Tor exit nodes. Some consider VPN over Tor more secure because it maintains anonymity throughout the entire process (assuming you pay for your VPN anonymously). Although the official Tor Project advises against VPN over Tor, both methods are superior to not using a VPN at all.
The major caveat is speed. Due to all the nodes that your traffic passes through, Tor by itself significantly limits bandwidth. Adding a VPN to it, even a fast one like IPVanish will make it even slower, so please be patient.
I2P
I2P is an alternative anonymous network to Tor. Unlike Tor, however, it cannot be used to access the public internet. It can only be used to access hidden services specific to the I2P network. I2P cannot be used to access .onion sites because it is a completely separate network from Tor. Instead, I2P uses its own brand of hidden sites called eepsites.
So why would you use I2P instead of Tor? After all, its much less popular, cant be used to access normal websites, and isnt as easy to use, among other disadvantages. Both rely on a peer-to-peer routing structure, combined with layered encryption to make browsing private and anonymous.
I2P does have a few advantages, though. Its much faster and more reliable than Tor for a number of technical reasons. The peer-to-peer routing structure is more advanced, and it does not rely on a trusted directory to get route information. I2P uses one-way tunnels, so an eavesdropper can only capture outbound or inbound traffic, not both.
Setting up I2P requires more configuration on the users part than Tor. I2P must be downloaded and installed, after which configuration is done through the router console. Then individual applications must each be separately configured to work with I2P. On a web browser, youll need to configure your browsers proxy settings to use the correct port.
Freenet
Like I2P, Freenet is a self-contained network within the network that cant be used to access sites on the public web. It can only be used to access the content uploaded to the Freenet, which is a peer-to-peer distributed data store. Unlike I2P and Tor, you dont need a server to host content. Once you upload something, it stays there indefinitely even if you stop using Freenet, so long as it is popular.
Freenet allows users to connect in one of two modes: darknet and opennet. Darknet mode allows you to specify who your friends are on the network and only connect and share content with them. This allows groups of people to create closed, anonymous networks made up solely of people they know and trust.
Alternatively, users can connect in opennet mode, which automatically assigns peers on the network. Unlike darknet mode, opennet uses a handful of centralized servers in addition to the decentralized peer-to-peer network.
Configuration is fairly straightforward. Just download, install, and run. When you open your default browser, Freenet will be ready and running through its web-based interface. Note you should use a separate browser than the one you normally use to help ensure anonymity.
Freenet is still an experiment designed to resist denial-of-service attacks and censorship.
Dark Web stats and facts
- The Dark Web, often associated with illegal activities, has seen a surge in activity in 2023.
- Over 2.5 million daily visitors accessed the Dark Web, with more than half involved in illicit activities.
- In April 2023, the number of daily visitors spiked to 2.7 million.
- The Dark Web has become a hub for threat actors, with an estimated $1.5 billion changing hands in 2022.
- Illicit drug sales on the Dark Web are projected to grow by 15% annually.
- Despite the shutdown of Hydra Market in 2022, new darknet markets have emerged.
- The volume of malware on the Dark Web has increased, posing challenges for cybersecurity teams.
- The Dark Web Price Index 2023 shows a decrease in pricing for most items and services due to increased competition.
- Despite efforts to dismantle illegal marketplaces, the Dark Web economy remains robust. No long-term decrease in sales volume has been reported, indicating a strong demand for illicit goods and services.
How to get on the Dark Web FAQs
Are sites on the dark web illegal to use and visit?
The dark web contains much of the internets illicit content, ranging from drug trafficking to child pornography sites. Accessing such content is illegal and should be avoided.
That being said, not everything on the dark web is illegal. Many dark websites are perfectly legal and safe to use and, in many cases, are better for your privacy than clear websites.
Why was the dark web created in the first place?
The Tor network was created by the US military in the 1990s for anonymous communication between spies over the internet. That effort was never fully realized, but the US military published the code under a free license in 2004. Researchers from the Electronic Frontier Foundation and other groups continued its development and launched the Tor project in 2006 as a tool for journalists, activists, and whistleblowers.
Will visiting the dark web attract attention?
Connecting to the Tor network might raise eyebrows depending on who and where you are. Although data sent through Tor cant be tracked or decrypted, your internet service provider and network administrator can still see that youre using Tor. For this reason, we recommend pairing Tor with a VPN. The VPNs encryption will hide from your ISP the fact that youre using Tor.
Can I use Tor to browse the surface web?
Yes! One of the great things about Tor is that it can be used to access both the dark web and the surface web. Just note that although youll be anonymous, you wont have the speed or convenience of a direct connection, and some sites might block you outright.
Is my phone number on the dark web?
Yes, your phone number may be on the dark web. The best way to find out is to check the Have I Been Pwned (HIBP) website. This website allows you to type in your email address or phone number and see if its been compromised in any data breaches. If your information has been compromised, then its likely that your phone number is also on the dark web.
Do I need a VPN if I access the dark web on my phone?
Yes, you definitely need a VPN if you want to access the dark web on your phone. This is because the dark web is full of potentially dangerous content, and a VPN will help keep your identity and personal information safe. Without a VPN, you could be putting yourself at risk of being hacked or scammed.
There are many different ways to access the dark web, but navigating it can be tricky and dangerous if you dont know what youre doing. A VPN will give you an extra layer of protection and anonymity, making it much safer to explore the dark web.
Is porn available on the dark web?
There is no doubt that porn is widely available on the dark web. In fact, there is an entire section of the dark web dedicated to pornographic content. However, it is important to note that not all of this content is legal.
The dark web provides a space for people to access and share all sorts of illegal and explicit material without judgment or censorship.
In fact, much of it may be illegal under your jurisdiction. As such, you should exercise caution when accessing any unofficial dark websites.
Why isn't the dark web stopped or shut down?
There are a few reasons why the dark web isnt stopped or shut down. First, its difficult to track and monitor activity on the dark web since much of it is encrypted.
Second, shutting down or controlling access to the dark web would be a huge undertaking and could have unintended consequences. Finally, many people consider the dark web a necessary tool for privacy and freedom of speech.
Can my ISP see that I am accessing the dark web?
Installing the Tor Browser is the best way to access the dark web. Note that your ISP will be able to see youre connected to Tor. However, your online activity is encrypted and hidden from view thanks to Tors onion routing. This means your ISP cant see that youre accessing the dark web (or indeed, the specific sites youre accessing).
You wont be able to search the dark web with a regular browser (such as Chrome or Firefox). Besides, your online activity on such browsers is visible to your ISP unless you connect to a VPN service.
Can you go to the dark web with incognito mode?
Yes, you can access the dark web in incognito mode. However, it is essential to note that this does not provide any extra security for your device or information.
The incognito mode only prevents the browser from storing history and cookies; your IP address and other details are still visible to anyone on the network. Therefore, using a different browser, such as Tor, is recommended to browse safely and securely on the dark web.
Is the dark web actually anonymous?
Yes, the dark web is indeed anonymous. This means that the identities and locations of darknet users are hidden from public view and remain anonymous, even when interacting with other users or engaging in any online activity.
The technology behind this anonymous connection is known as onion routing, which utilizes a layered approach to obscure data and protect users locations on the network.
Identifying specific individuals who use the dark web can be quite tricky. However, we advise connecting to one of our recommended VPN services to stay anonymous.
See also: The best VPNs for Tor and how to Download the Tor Browser